GPS spoofer countermeasure effectiveness based on signal strength, noise power, and C/N0 measurements - Jafarnia Jahromi - 2012 - International Journal of Satellite Communications and Networking - Wiley Online Library
Detection of Spoofing Attack using Machine Learning based on Multi-Layer Neural Network in Single-Frequency GPS Receivers | The Journal of Navigation | Cambridge Core
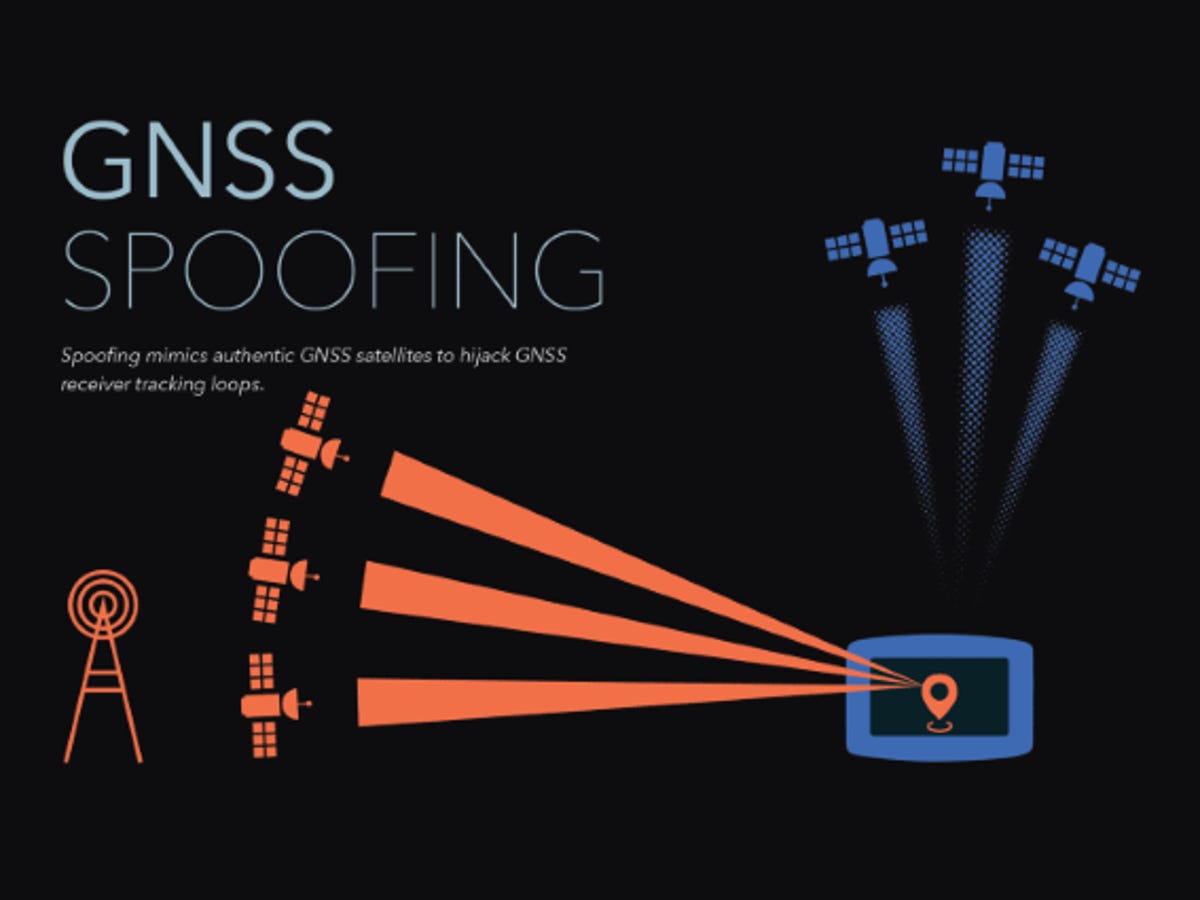
In)Feasibility of Multi-Frequency Spoofing - Inside GNSS - Global Navigation Satellite Systems Engineering, Policy, and Design
Sensors | Free Full-Text | Impact Assessment of GNSS Spoofing Attacks on INS/GNSS Integrated Navigation System
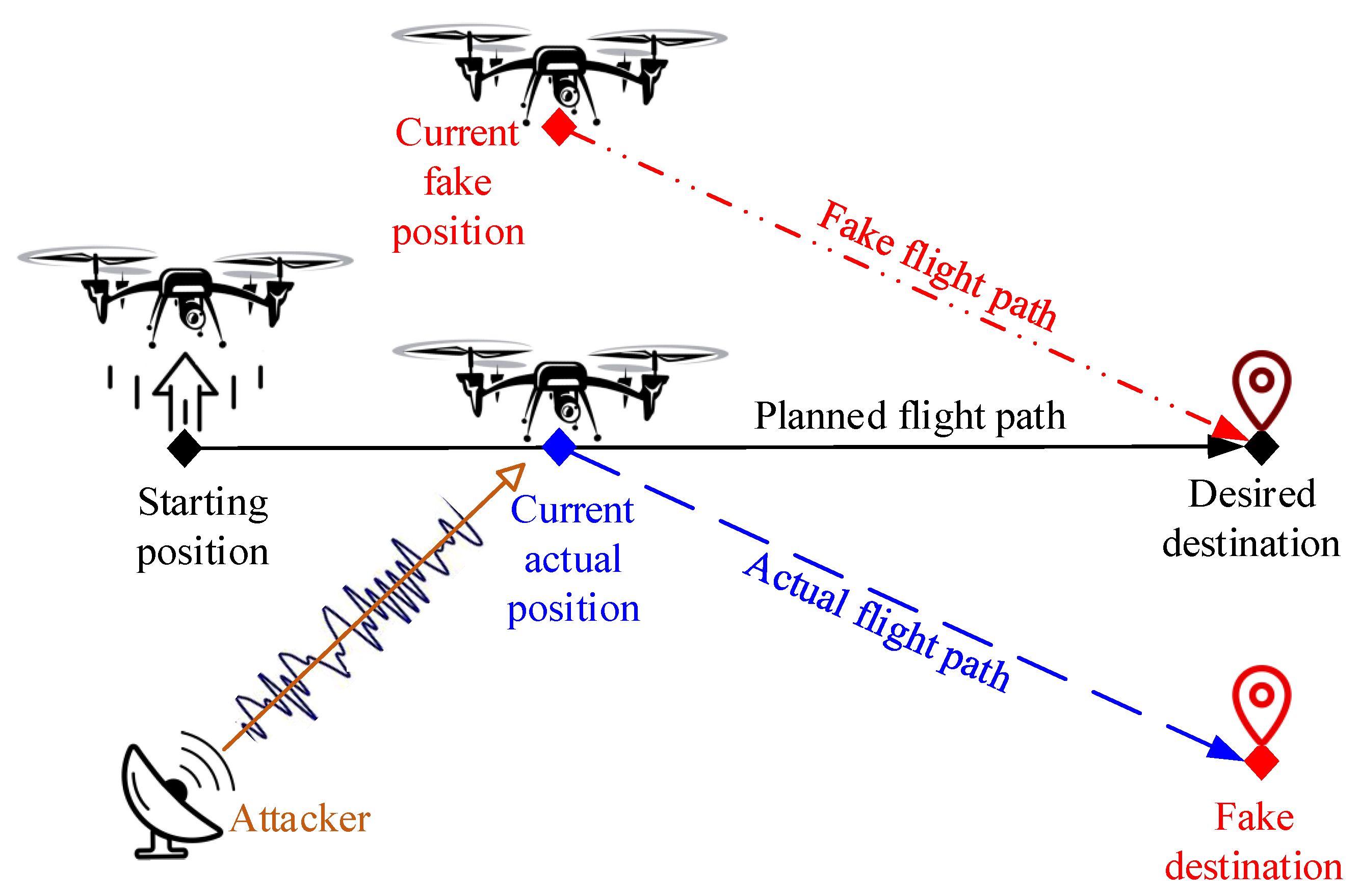
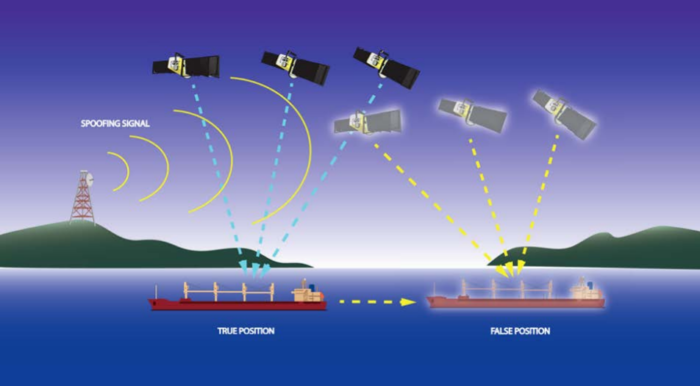
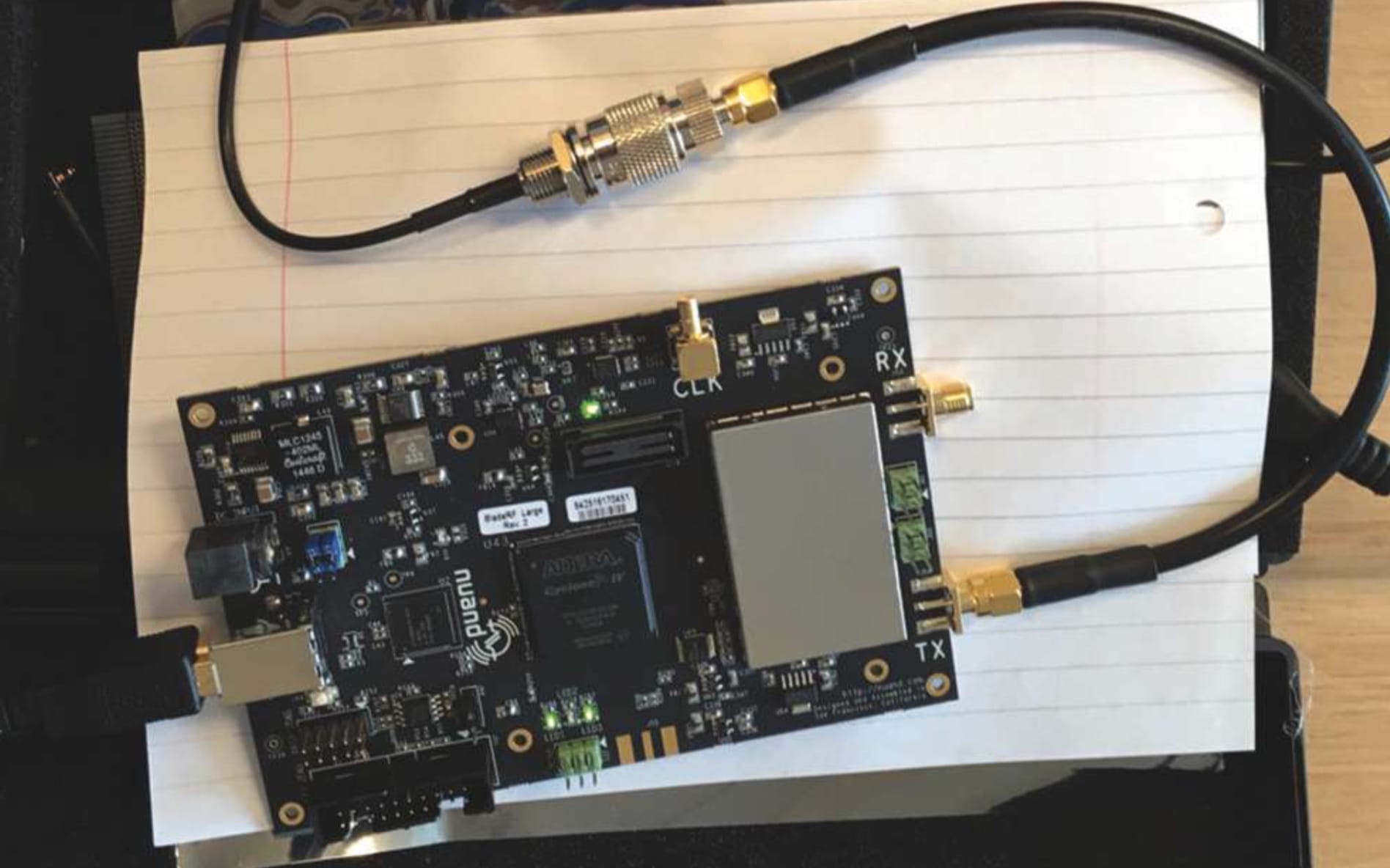
![On GPS spoofing of aerial platforms: a review of threats, challenges, methodologies, and future research directions [PeerJ] On GPS spoofing of aerial platforms: a review of threats, challenges, methodologies, and future research directions [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2021/cs-507/1/fig-4-2x.jpg)
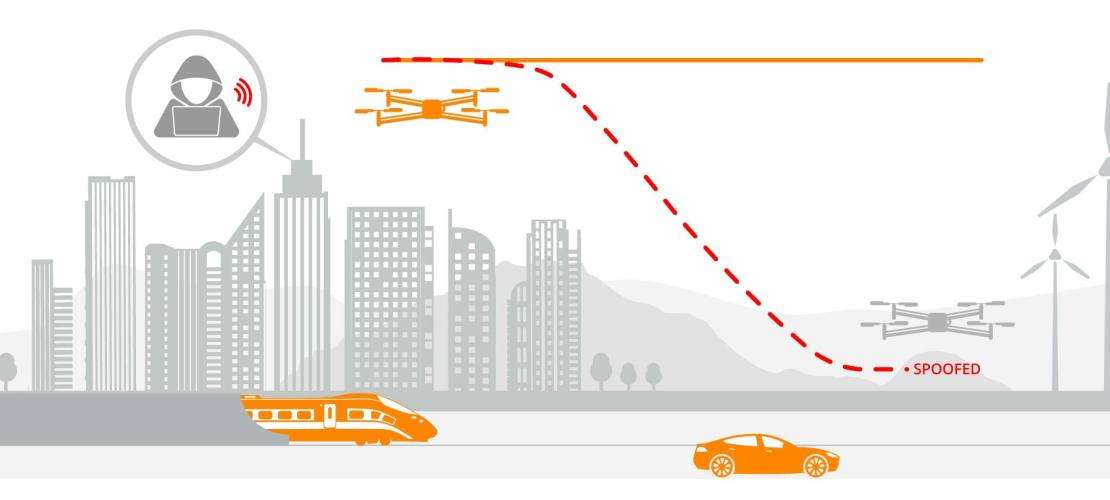
On GPS spoofing of aerial platforms: a review of threats, challenges, methodologies, and future research directions [PeerJ]

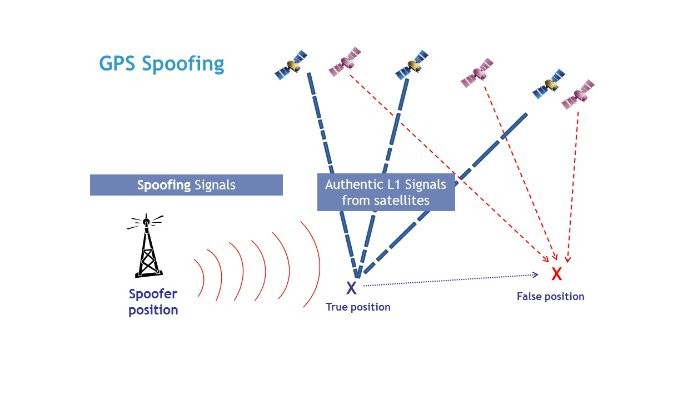
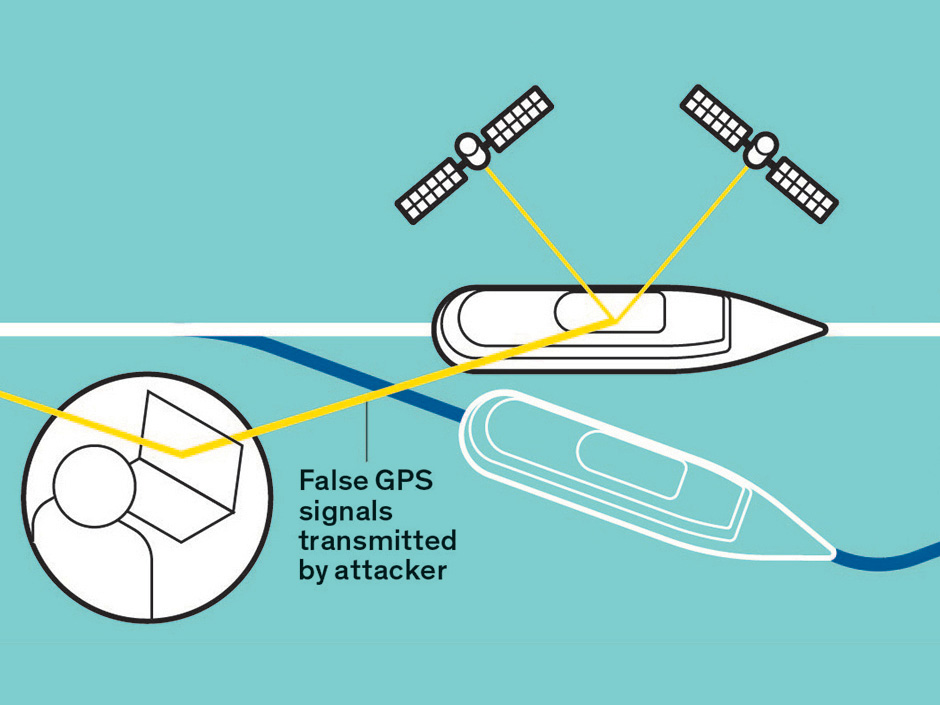
A GPS spoofing scenario: Spoofer tries to deviate UAV from the main... | Download Scientific Diagram

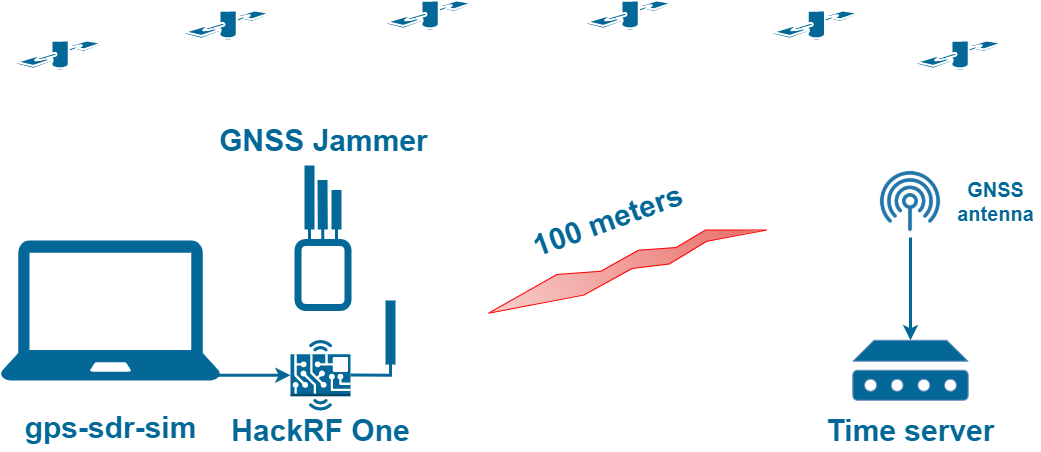
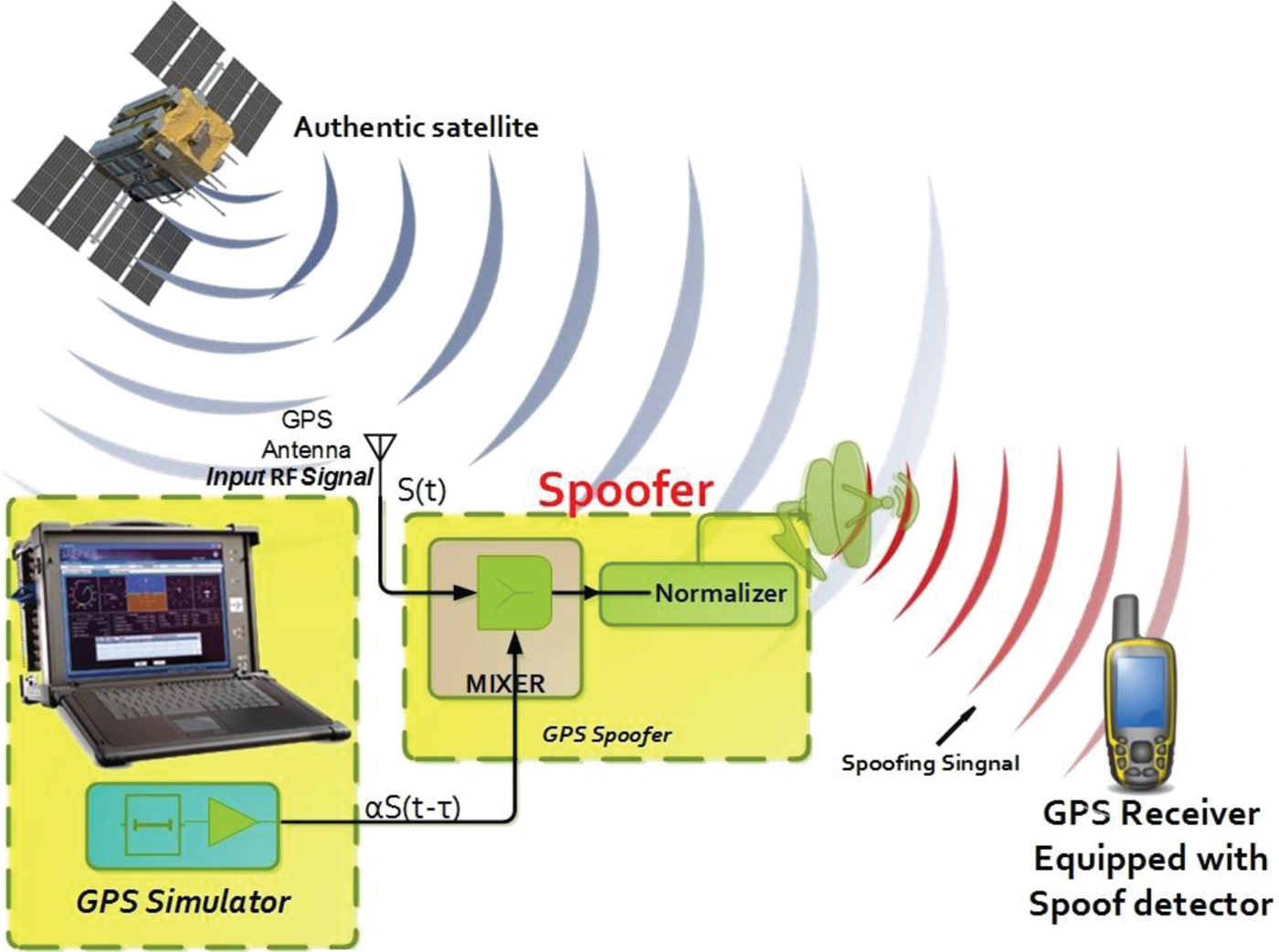
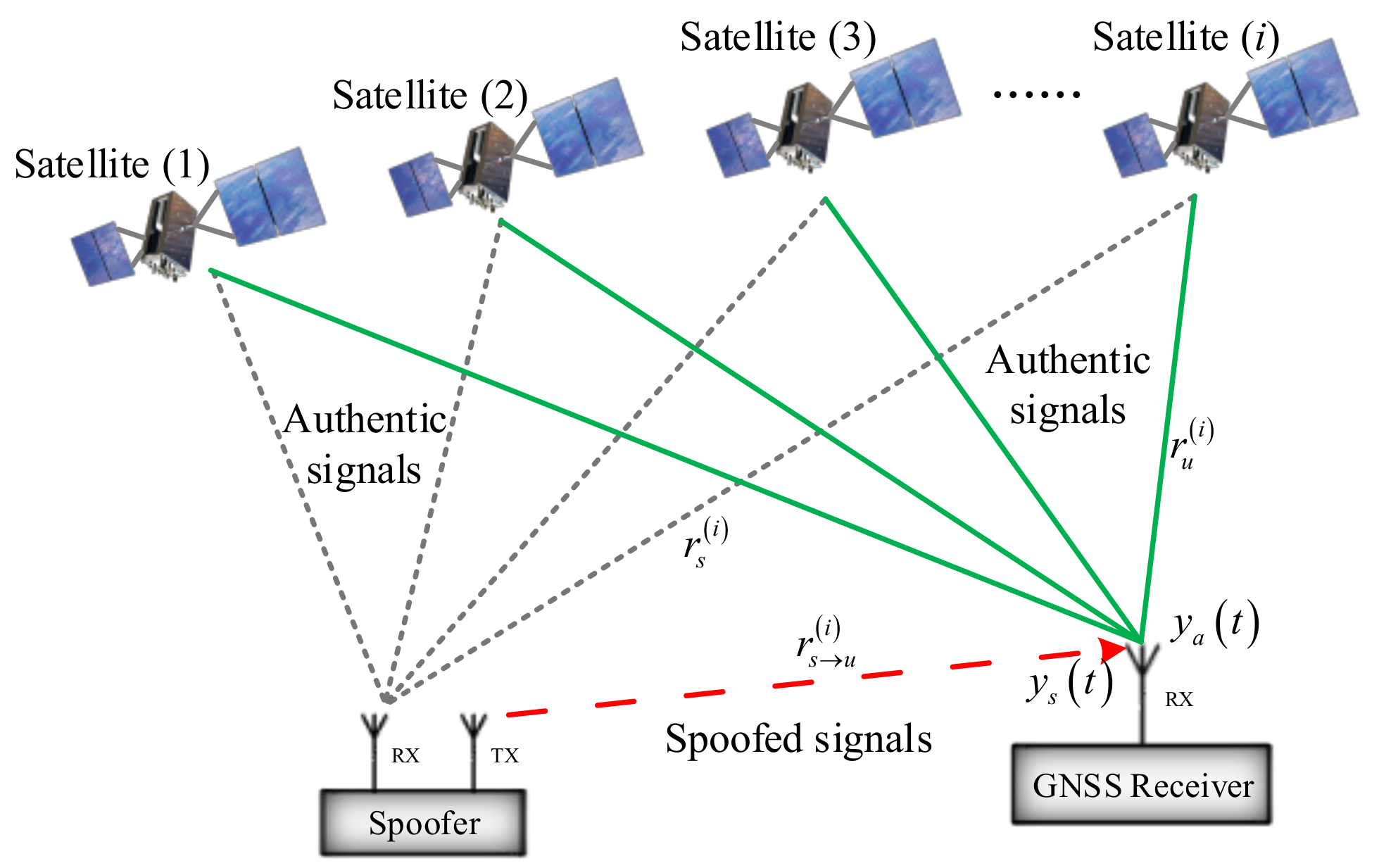
Spoofing environment. It is assumed that the spoofer receives authentic... | Download Scientific Diagram